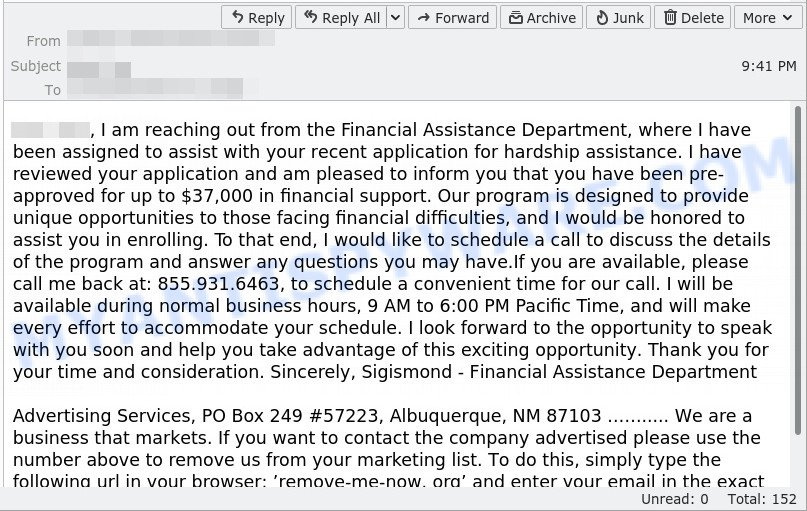
In an age where digital communication is paramount, our inboxes are flooded with a myriad of emails, including those that attempt to lure us into financial peril. Among these are craftily designed email scams purportedly from ‘financial hardship departments’. These phishing expeditions aim to trick you into divulging sensitive personal and financial information. Falling prey to such schemes can have dire consequences, but fear not, as there are practical steps one can take to fortify their defenses against these fraudulent acts.
Vigilance in Verifying Sender Identity
It’s imperative to establish the legitimacy of any email claiming to originate from a financial institution or hardship program. Often, scammers will mimic official communication to gain your trust.
Detailed Steps:
- Inspect the sender’s email address: Legitimate emails from financial institutions will typically use a domain name corresponding with the institution’s official website.
- Look for generic greetings: Scammers tend to use general salutations such as “Dear customer” rather than addressing you by name.
- Research contact information: Verify the contact details in the email signature by comparing them with those on the official website of the company.
- Use official communication channels: If in doubt, reach out to the institution through official channels to confirm the email’s authenticity.
Summary:
Double-checking the sender’s details empowers you to discern genuine communications from fraudulent ones. The downside is that it requires time and diligence.
Smart Password Practices
Weak passwords are like leaving your digital door unlocked. Creating robust, unique passwords for different accounts can thwart scammers’ attempts to access your information.
Detailed Steps:
- Create complex passwords: Use a mix of upper and lower case letters, numbers, and symbols.
- Avoid personal information: Don’t include easily guessable details like your birthdate.
- Update regularly: Change passwords every three to six months and after any suspicion of a breach.
- Use a password manager: To keep track of numerous complex passwords, consider using a password manager.
Summary:
Strong passwords are vital for online security, but remembering them can be a challenge without the help of a password manager, which some may be uncomfortable using.
Caution with Links and Attachments
Scam emails often include malicious links or attachments designed to steal your personal information or infect your computer with malware.
Detailed Steps:
- Hover over links: Place your cursor over any link in the email to preview the URL before clicking.
- Avoid opening unexpected attachments: Unless you can verify the sender and were expecting an attachment, do not open it.
- Use antivirus software: Ensure your antivirus software is up-to-date and scan any downloaded files.
- Check for HTTPS: Before entering any personal information, ensure the website is secured with HTTPS, indicated by a padlock icon beside the URL.
Summary:
Exercising caution with links and attachments can significantly reduce scam risks, although it can lead to inconvenience and may hinder the opening of legitimate attachments without careful screening.
Educational Awareness
Understanding common scam tactics enables you to identify and avoid them. Knowledge is a powerful tool against scammers.
Detailed Steps:
- Stay informed: Regularly read articles and updates on known email scam tactics.
- Attend workshops: Participate in cybersecurity workshops for hands-on learning.
- Share with others: Discuss your learnings with friends and family to spread awareness.
- Sign up for alerts: Enroll in scam alert services offered by various consumer protection agencies.
Summary:
Educating yourself and your network can help everyone stay a step ahead of scammers. The possibility of information overload or becoming overly cautious are potential downsides to consider.
Regular Account Monitoring
Frequent review of your financial transactions can help you spot irregularities indicative of fraudulent activity.
Detailed Steps:
- Check statements: Regularly examine your bank and credit card statements for unauthorized charges.
- Set alerts: Enroll in transaction alerts provided by your bank to stay informed of account activity.
- Report anomalies: Contact your financial institution immediately if you detect any unusual activity.
- Use secure networks: While monitoring accounts, ensure you’re on a secure network, not public Wi-Fi.
Summary:
Regular monitoring is a key preventive measure against fraud but can sometimes lead to false alarms causing unnecessary panic.
Social Media Savviness
Scammers often gather personal details from social media to make their phishing emails more convincing.
Detailed Steps:
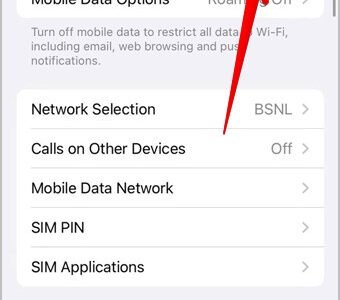
- Adjust privacy settings: Limit the amount of personal information visible to the public.
- Think before sharing: Be cautious about the personal information you share online.
- Recognize friend requests: Accept connection requests only from people you know.
- Secure your profile: Regularly update your social media accounts with strong, unique passwords.
Summary:
Protecting your personal information on social media is effective for avoiding targeted scams, though it requires ongoing vigilance and may limit your online social interactions.
Email Filters and Security Settings
Using email filters and enhancing security settings can automatically weed out many fraudulent emails.
Detailed Steps:
- Enable spam filters: Set up your email account to detect and filter out potential spam.
- Mark as spam: Help your email provider identify scams by marking suspicious emails as spam.
- Update security settings: Regularly review and enhance your email account’s security settings.
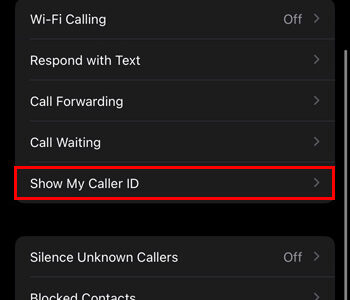
- Use two-factor authentication: Add an extra layer of security to your email account by enabling two-factor authentication.
Summary:
Proactive use of email security options will reduce scam exposure, however, configured filters may occasionally block legitimate emails, requiring manual checks of your spam folder.
Financial Literacy
A solid understanding of financial practices can make it easier to spot inconsistencies in scam emails claiming to be from financial hardship departments.
Detailed Steps:
- Know standard procedures: Financial institutions have set protocols for contacting customers, which seldom include unsolicited email requests for sensitive information.
- Read the fine print: Familiarize yourself with the policies of your financial service providers.
- Watch for red flags: Be wary of emails with urgent language, demanding immediate action regarding your finances.
- Verify offers: Before acting on any offers or demands, verify their validity with your financial institution.
Summary:
Financial literacy helps you recognize unusual requests, though acquiring it takes time and diligence.
Trust Your Instincts
Sometimes, a simple ‘gut feeling’ that something isn’t right can be your first line of defense against email scams.
Detailed Steps:
- Pause and reflect: If an email makes you uneasy, take a moment to ponder why.
- Seek second opinions: Discuss suspicious emails with trusted friends or advisors.
- Listen to skepticism: If something feels off, it likely is, and warrants further investigation.
- Err on the side of caution: When in doubt, it’s safer to ignore or delete the email than to engage with it.
Summary:
Trusting your instincts can be incredibly protective against scams, with minimal downsides, provided that you balance intuition with rational verification steps.
Keep Software Updated
Outdated software can have vulnerabilities that scammers exploit to gain access to your system.
Detailed Steps:
- Enable automatic updates: Configure your operating system and applications to update automatically.
- Check updates manually: Regularly check for updates to ensure your software is current.
- Restart when required: Some updates need a system reboot; don’t ignore prompts to restart your computer.
- Use a reliable source: Always download software updates directly from the official provider.
Summary:
Maintaining up-to-date software is crucial for security; however, occasionally, new updates may cause compatibility issues or system glitches.
Backup Your Data
Regularly backing up your data ensures that, in the event of a successful scam leading to data compromise, you have a safety net.
Detailed Steps:
- Use external drives: Store backups on external hard drives or USB sticks.
- Cloud backups: Consider using a cloud service for secure, off-site backups.
- Encrypt your backups: Protect stored data from unauthorized access with encryption.
- Update your backups: Back up your data frequently to ensure it’s current.
Summary:
Backup practices provide peace of mind and data security, but they require discipline and understanding of encryption and may incur costs for cloud storage services.
Conclusion
Bracing yourself against the dread of financial hardship email scams may seem daunting, but the power lies in your ability to institute these defenses. Each tip serves as a layer of armour between scammers and your personal information, creating a formidable barrier. Navigating the digital landscape safely is an ongoing journey, one that evolves as rapidly as the threats. By staying informed and proactive, each step forward you take is a stride in securing your online experience.
FAQs
-
How can you tell if an email is actually a scam?
You can spot a scam by looking for red flags such as generic greetings, grammatical errors, requests for sensitive information, and urgent or threatening language. Always verify the sender’s email address and compare it to official contact information. -
What should you do if you’ve clicked on a link in a phishing email?
Immediately disconnect your device from the internet to prevent further data leaks. Run a full system antivirus scan and change passwords for your accounts. Monitor your financial statements for any unauthorized transactions and consider notifying your bank. -
Why is it important to use different passwords for different accounts?
Using unique passwords for each account ensures that if one account is compromised, your other accounts remain secure. It prevents a single breach from cascading into a full-fledged identity theft scenario.